As organizations rapidly adopt cloud computing, traditional perimeter-based security models are becoming obsolete. In distributed environments where users, devices, and applications operate across locations, assuming trust based on network position is no longer safe.
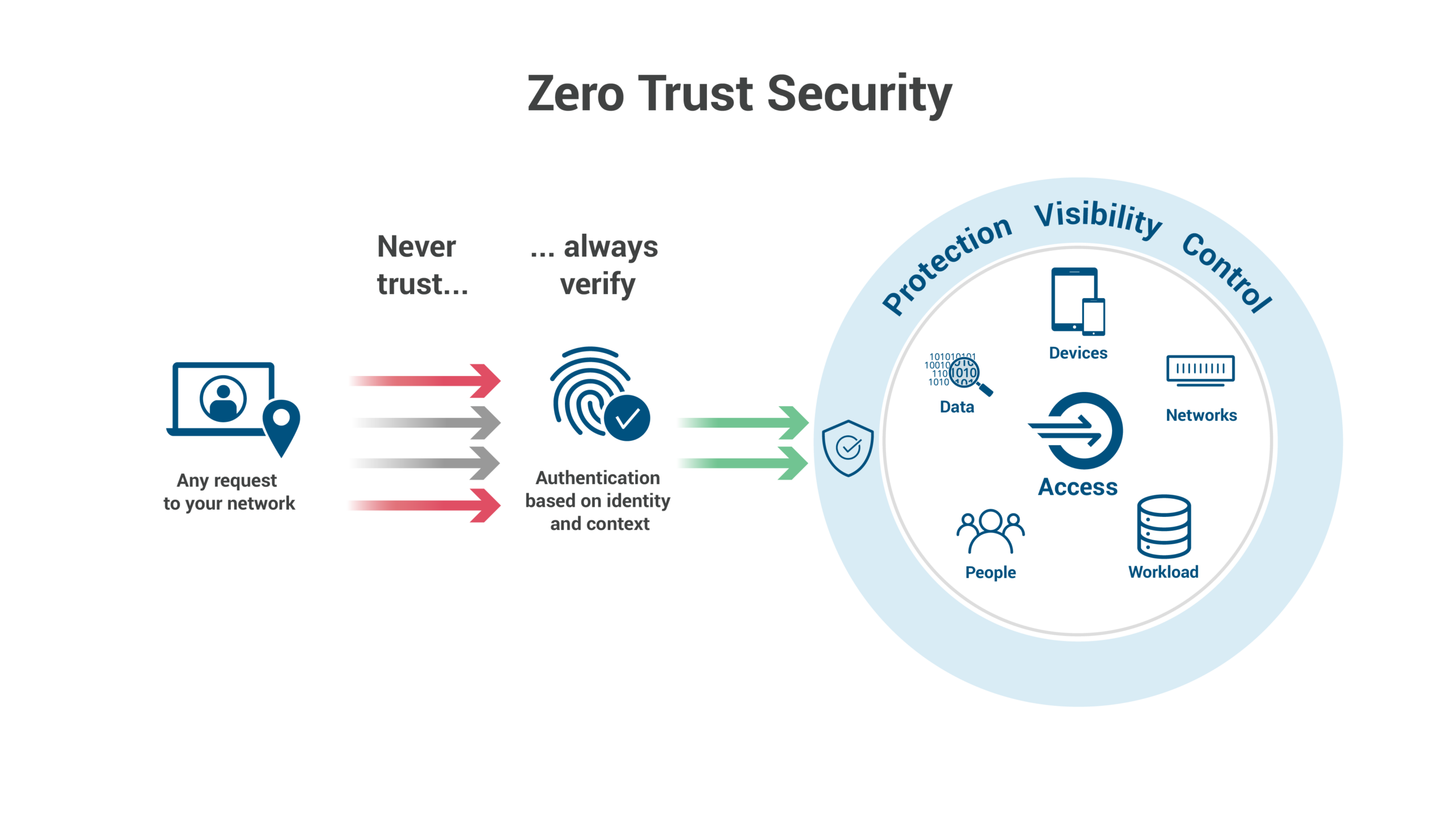
Zero Trust Architecture (ZTA) is a modern security framework built on the principle: “Never trust, always verify.” In 2026, Zero Trust has become a foundational requirement for protecting sensitive data, preventing breaches, and meeting compliance standards in cloud-first enterprises.
WHAT IS ZERO TRUST ARCHITECTURE?
Zero Trust assumes no user, device, or system is trusted by default — even inside the network. Every access request must be authenticated, authorized, encrypted, and continuously validated.
WHY ZERO TRUST IS CRITICAL IN THE CLOUD
Cloud environments lack traditional boundaries. Users access systems remotely, applications run across multiple platforms, and APIs connect services globally.
Key drivers:
• Remote and hybrid work
• Identity-based attacks
• Multi-cloud complexity
• API-driven systems
• Insider threats
• Regulatory pressure
CORE PRINCIPLES
1) Verify Explicitly
Authenticate using identity, device health, location, behavior, and risk signals. Multi-Factor Authentication (MFA) is essential.
2) Enforce Least-Privilege Access
Users receive only necessary permissions, reducing attack surface and limiting damage from compromised accounts.
3) Assume Breach
Security designs assume attackers may already be present, focusing on containment and rapid response.
KEY COMPONENTS
Identity and Access Management (IAM):
• MFA enforcement
• Role-based access control
• Single sign-on
• Privileged account monitoring
• Just-in-time access
Device Security:
• Compliance checks
• Endpoint protection
• Mobile device management
• Patch enforcement
Network Micro-Segmentation:
• Isolates workloads
• Prevents lateral movement
• Protects critical systems
Data Protection:
• Encryption at rest and in transit
• Strong key management
• Data classification
• Masking/tokenization
Continuous Monitoring:
• Behavioral analytics
• Anomaly detection
• Centralized logging
• Threat intelligence
Application and API Security:
• Strong authentication
• API gateways
• Rate limiting
• Input validation
IMPLEMENTATION GUIDE
Step 1: Assess Current Security Posture
Identify sensitive data, access patterns, devices, and vulnerabilities.
Step 2: Define Protect Surfaces
Focus on critical assets such as sensitive data, core applications, and key services.
Step 3: Strengthen Identity Controls
Implement MFA, conditional access, identity federation, and passwordless options.
Step 4: Implement Least Privilege
Use granular permissions, temporary access, and regular reviews.
Step 5: Deploy Micro-Segmentation
Segment workloads using software-defined controls and security policies.
Step 6: Enhance Visibility
Use SIEM platforms, centralized dashboards, and automated alerts.
Step 7: Automate Security
Automate policy enforcement, incident response, and compliance checks.
Step 8: Continuous Testing
Conduct audits, penetration tests, and incident simulations regularly.
COMMON CHALLENGES
• Legacy system compatibility
• Implementation complexity
• Skill shortages
• Cultural resistance
• Multi-cloud integration issues
INDUSTRIES THAT BENEFIT MOST
• Banking and finance
• Healthcare
• Government
• Defense
• Telecommunications
• Technology companies
• Critical infrastructure
BENEFITS
• Reduced breach risk
• Protection against ransomware
• Compliance readiness
• Secure remote access
• Improved visibility
• Protection from insider threats
• Increased customer trust
FUTURE TRENDS
• AI-driven adaptive security
• Passwordless authentication
• Identity-first platforms
• Edge security integration
• Automated compliance
FINAL THOUGHTS
Zero Trust Architecture is essential for modern cloud security. By shifting to identity-centric, continuously verified access models, enterprises can protect critical assets while enabling innovation and growth in a distributed digital landscape.