As organizations continue migrating critical workloads to the cloud, security has become a top strategic priority. In 2026, enterprises face an evolving threat landscape driven by sophisticated cyberattacks, AI-powered malware, ransomware campaigns, and increasingly strict regulatory requirements.
Modern cloud environments offer powerful capabilities — but also introduce new security challenges. Unlike traditional on-premise systems, cloud security follows a shared responsibility model, meaning both the provider and the customer play critical roles.
UNDERSTANDING THE CLOUD SECURITY LANDSCAPE IN 2026
Cloud adoption is now mainstream across industries such as finance, healthcare, government, retail, and manufacturing. Attackers increasingly target cloud misconfigurations, identity vulnerabilities, and exposed APIs rather than infrastructure itself.
Key trends shaping cloud security:
• Identity-based attacks
• AI-driven threat detection
• Multi-cloud complexity
• Zero Trust architectures
• Compliance requirements
• Supply chain risks
• Data sovereignty concerns
1) IMPLEMENT A ZERO TRUST SECURITY MODEL
Zero Trust assumes no user or device is trusted by default.
Key principles:
• Continuous verification
• Least-privilege access
• Micro-segmentation
• Device validation
• Context-aware controls
2) STRENGTHEN IDENTITY AND ACCESS MANAGEMENT (IAM)
Best practices:
• Enforce Multi-Factor Authentication (MFA)
• Role-based access control (RBAC)
• Credential rotation
• No shared accounts
• Privileged access monitoring
3) ENCRYPT DATA EVERYWHERE
Types:
• Data-at-rest
• Data-in-transit
• Data-in-use
Robust key management is essential.
4) SECURE CLOUD CONFIGURATIONS
Common risks:
• Public storage exposure
• Open ports
• Weak policies
• Disabled logs
Use automated scanning tools.
5) CONTINUOUS MONITORING AND THREAT DETECTION
Capabilities:
• Centralized logging
• SIEM systems
• Real-time alerts
• Behavioral analytics
• Automated response
6) NETWORK SECURITY AND SEGMENTATION
Best practices:
• Virtual Private Clouds
• Subnet isolation
• Web Application Firewalls
• Private endpoints
• Strict traffic rules
7) SECURE CONTAINERS AND KUBERNETES
Measures:
• Image scanning
• Trusted registries
• Runtime protection
• Least privilege
• Secure orchestration
8) BACKUP AND DISASTER RECOVERY
Actions:
• Automated backups
• Isolated storage
• Recovery testing
• Defined RTO/RPO
• Cross-region redundancy
9) COMPLIANCE AND DATA GOVERNANCE
Includes GDPR, HIPAA, PCI DSS, ISO 27001.
Key components:
• Data classification
• Audit trails
• Retention policies
• Access control
10) AI-DRIVEN SECURITY TOOLS
AI enables:
• Threat prediction
• Anomaly detection
• Automated response
• Fraud prevention
11) SECURE APIs
Best practices:
• API gateways
• Strong authentication
• Rate limiting
• Input validation
• Monitoring
12) DEVSECOPS
Integrate security into CI/CD:
• Automated testing
• Vulnerability scanning
• IaC security checks
• Policy enforcement
13) RANSOMWARE PROTECTION
Strategies:
• Immutable backups
• Network isolation
• Endpoint security
• User training
• Incident plans
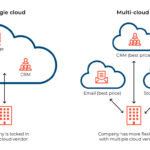
14) MULTI-CLOUD SECURITY
Ensure consistent controls across providers:
• Unified platforms
• Central identity
• Standard policies
• Cross-cloud monitoring
WHY CLOUD SECURITY MATTERS
Strong security provides:
• Risk reduction
• Compliance
• Customer trust
• Brand protection
• Business continuity
FINAL THOUGHTS
Cloud security in 2026 requires a proactive, holistic approach combining technology, processes, and people. With strong identity controls, encryption, monitoring, and governance, enterprises can confidently scale while protecting critical assets.